Security technology is not enough
 Cyber security plays an increasingly important role in the design and development of every category of engineering project, and at the same time government and multinational bodies are coming together to create global strategies to tackle the threat, says Kevin Fuller, Security & Risk Consulting Practice Leader, Burns & McDonnell
Cyber security plays an increasingly important role in the design and development of every category of engineering project, and at the same time government and multinational bodies are coming together to create global strategies to tackle the threat, says Kevin Fuller, Security & Risk Consulting Practice Leader, Burns & McDonnell
Hostile cyber-attack is a Tier 1 risk to the UK, according to the National Security Risk Assessment, sitting alongside international military crises, terrorism and major accidents or natural hazards.
In the UK, the National Cyber Security Strategy 2016 to 2021 aims to make the UK one of the safest places in the world to live and work online. Meanwhile, the EU’s Network and Information Security directive sets specific cyber security requirements for operators of essential services, which includes the energy sector.
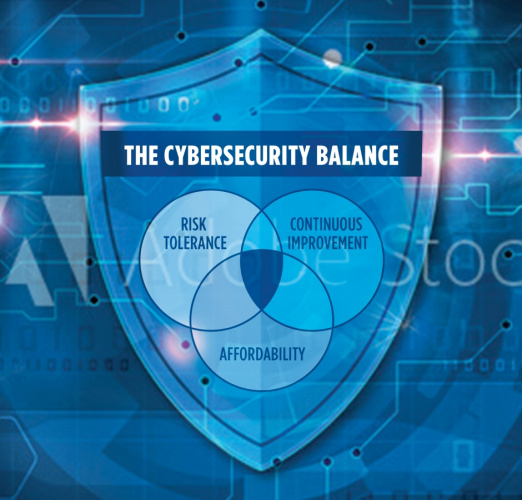
In this context, businesses need to be more prepared than ever to devote significant investment and resources to their security frameworks and capabilities. Here are some of the factors you should consider to ensure that you have a robust cyber security framework that protects your business, your employees and your customers for the long term. Bear in mind that balance is vitally important for a well-designed cyber security programme. Just as a healthy company requires a balanced budget to operate effectively, a properly functioning cybersecurity programme requires similar equilibrium.
Register now to continue reading
Thanks for visiting The Engineer. You’ve now reached your monthly limit of premium content. Register for free to unlock unlimited access to all of our premium content, as well as the latest technology news, industry opinion and special reports.
Benefits of registering
-
In-depth insights and coverage of key emerging trends
-
Unrestricted access to special reports throughout the year
-
Daily technology news delivered straight to your inbox










Water Sector Talent Exodus Could Cripple The Sector
Maybe if things are essential for the running of a country and we want to pay a fair price we should be running these utilities on a not for profit...